CCIE Security Certification Training
Discover the depths of CCIE Security Technology. Join us now to gain comprehensive insights into CCIE Security technology from a seasoned professional.
![]() 5 out of 5 based on 101 user reviews. |
5 out of 5 based on 101 user reviews. |  |
|  |
|  |
| 
Enquire Now
Accreditations & Affiliations
Training Features
Best CCIE Security Institute in Delhi NCR
Join Best CCIE SECURITY Online Training in Delhi, CCIE SECURITY Online Training Course in Delhi, CCIE SECURITY Online Training Institute in Noida
The Cisco Certified Internetwork Expert Security (CCIE Security) program recognizes candidates, who have the skills and knowledge to implement, maintain and support extensive Cisco Network Security Solutions using the latest industry best practices and technologies. The CCIE Security certification shows the skills required by network engineers to operate, plan and troubleshoot complex, complicated or converged network infrastructures on a wide variety of networking equipment.
CCIE Security training offers multiple job opportunities to candidates across the world. Excellent pay packages with best technical profiles are the characteristics of CCIE Security experts in reputed MNCs. These are offered to deserving candidates having the expertise in CCIE Security training.
So if candidates follow the hierarchy of gaining the certifications right from the associate level (CCNA) to the expert level (CCIE) then success will surely be achieved. The most popular job designations for CCIE certified employees are
- Network Engineer
- Sr. Network Engineer
- Security Consultant (Computing /Information Technology/Networking)
- Network Administrator (IT)
- Systems Engineer (Computer Networking/IT)
- Network Security Engineer
- Senior Systems Engineer (Computer Networking/IT)
Candidates after completion of B.E/B.Tech/BCA/MCA degree can opt for CCIE Security training. Candidates completing bachelor’s course in general stream are also considered eligible, subject to eligibility is other criteria.
There are no formal prerequisites for CCIE certification. Instead, candidates have to pass a written qualification exam firstly and then the corresponding hands-on lab exam. After completion of the course, candidates need to qualify in written examination of 3 hours duration, followed by a lab examination of 8 hours duration. Candidates are anticipated to have in-depth understanding and knowledge of the topics in the exam blueprints. Candidates are strongly encouraged to have 4-5 years of job experience before attempting the expert level certification.
CETPA is a training company, having excellence of 12 years in providing the engineering students with technical training as well as certification of 50+ technologies delivered by highly experienced instructors with extensive hands-on knowledge. CETPA has built a wide network of modern education centers in Lucknow, Roorkee, Dehradun, and Noida (Delhi-NCR). All centers are owned by the company to ensure impeccable standards and there are no franchise centers.
CETPA offers CCIE security training to students for a period of 4/6 weeks- 6 months. We also offer vocational CCIE security training and short term courses for the working employers to let them have more proficiency in CCIE Security. We offer our students with highest satisfaction and enhance the learning skill among them. Best infrastructure including online CCIE security training classes for the Indian as well as NRI students to equip them with high quality one-to- one interactive CCIE Security training to make them have real classroom feel. Some features of CETPA that differentiate them from others training companies are
- Complete understanding of the subject which will help building a firm base for the next training levels.
- Free usage of its advanced internetworking lab facilities for self-practices.
- Intensive Instructor facilitated learning.
- Free updates of new and upcoming technology.
- Extra sessions for LAB practice in presence of the instructor.
- Periodic tests for students during the course tenure of CCIE security training.
- Offering 100% authentic placement record.
- Step-1: CCIE Security Written Exam: It’s a 2 hour written exam that covers networking concepts and some equipment commands.
- Step-2: CCIE Security Lab Exam:It’s an 8 hour exam that will test the candidate’s ability to configure actual equipment and troubleshoot the network in a timed test situation.
During the period of recession, only the CCIE certified professionals enjoyed a tension-free environment in comparison to the unemployment and downsizing ratio across the world, this shows the high demand of CCIE Security Training in industry. CCIE security engineers are hired by corporation giants like
- CSS Corp Pvt. Ltd.
- Dell
- Allianz
- Cisco
- Capegamini
- HP
- Microsoft
- AES Corporation
- Apple
- Wipro and more...
- You will get better knowledge of programming and how to implement it for actual development requirements in the industrial projects and applications.
- Enhanced knowledge on the web development framework. Using this framework, you can develop dynamic websites swiftly.
- You will learn how to design, develop, test, support and deploy desktop, custom web, and mobile applications.
- Design and improve testing and maintenance activities and procedures.
- Design, implement and develop important applications in a CCIE-Security environment.
- Increased chances of working in leading software companies like Infosys, Wipro, Amazon, TCS, IBM and many more.
Professional growth, increased compensation and validation of the skill are the most popular reasons why individuals and professionals seek IT certifications. Keeping this in mind, we at CETPA provide you with certification in latest and innovative technologies to help you to reach your certification goals.
CETPA is the official Training partner of Oracle, Microsoft, Autodesk, Panasonic and Nuvoton and thus provides Training as per international standards and curriculum. CETPA proudly provides you certification in association with our training partners so that you can validate your domain specific technical skills. Certification from these big brands will help you in grabbing your dream job.
- Gives you an advantage while searching for a job and provide a competitive advantage over your competitors.
- Ensure knowledge and skill are up to date and can be applied to the job
- Provide credibility to those looking for a career in an IT domain.
- Offer fast track to career advancement
- Demonstrate level of competency
- Professional Credibility as well as it demonstrates your dedication and motivation to professional development.
- You are likely to stand out from the crowd and be considered to be successful in your positions.
- Represent a well-recognized and valued IT credential that increases marketability and competitive edge.
- Provide peace of mind with the confidence that certified employees have truly learned the skills necessary to do their jobs;
- Express valuable credentials to search for in prospective employees, and can help retain top performers when offered as an incentive;
- Offer a competitive advantage when the team is trained and certified regularly.
Talk To Advisor
MODE/SCHEDULE OF TRAINING:
| Delivery Mode | Location | Course Duration | Schedule (New Batch Starting) |
|---|---|---|---|
| Classroom Training (Regular/ Weekend Batch) | *Noida/ *Roorkee/ *Dehradun | 4/6/12/24 Weeks | New Batch Wednesday/ Saturday |
| *Instructor-Led Online Training | Online | 40/60 Hours | Every Saturday or as per the need |
| *Virtual Online Training | Online | 40/60 Hours | 24x7 Anytime |
| College Campus Training | India or Abroad | 40/60 Hours | As per Client’s need |
| Corporate Training (Fly-a-Trainer) | Training in India or Abroad | As per need | Customized Course Schedule |
Course Content
- OSI layers
- TCP/UDP/IP protocols
- LAN switching (for example, VTP, VLANs, spanning tree, and trunking)
- Routing protocols (for example, RIP, EIGRP, OSPF, and BGP)
- Basic functions and characteristics
- Security features
- Routing protocols (for example, RIP, EIGRP, OSPF, and BGP)
- Tunneling protocols
- GRE
- NHRP
- IPv6 tunnel types
- IP multicast
- PIM
- MSDP
- IGMP and CGMP
- Multicast Listener Discovery
- Wireless
- SSID
- Authentication and authorization
- Rogue APs
- Session establishment
- Authentication and authorization technologies
- Single sign-on
- OTPs
- LDAP and AD
- RBAC
- VPNs
- L2 vs L3
- MPLS, VRFs, and tag switching
- Mobile IP networks
- RSA
- RC4
- MD5
- SHA
- DES
- 3DES
- AES
- IPsec
- ISAKMP
- IKE and IKEv2
- GDOI
- AH
- ESP
- CEP
- TLS and DTLS
- SSL
- SSH
- RADIUS
- TACACS+
- LDAP
- EAP methods (for example, EAP-MD5, EAP-TLS, EAP-TTLS, EAP-FAST, PEAP, and LEAP)
- PKI, PKIX, and PKCS
- IEEE 802.1X
- WEP, WPA, and WPA2
- WCCP
- SXP
- MACsec
- DNSSEC
APPLICATION AND INFRASTRUCTURE SECURITY
- HTTP
- HTTPS
- SMTP
- DHCP
- DNS
- FTP and SFTP
- TFTP
- NTP
- SNMP
- Syslog
- Netlogon, NetBIOS, and SMB
- RPCs
- RDP and VNC
- PCoIP
- OWASP
- Manage unnecessary services
- Recognize and mitigate common attacks
- ICMP attacks and PING floods
- MITM
- Replay
- Spoofing
- Backdoor
- Botnets
- Wireless attacks
- DoS and DDoS attacks
- Virus and worm outbreaks
- Header attacks
- Tunneling attacks
- Software and OS exploits
- Security and attack tools
- Generic network intrusion prevention concepts
- Packet filtering
- Content filtering and packet inspection
- Endpoint and posture assessment
- QoS marking attacks
- Cisco Adaptive Security Appliance (ASA)
- Firewall functionality
- Routing and multicast capabilities
- Firewall modes
- NAT (before and after version 8.4)
- Object definition and ACLs
- MPF functionality (IPS, QoS, and application awareness)
- Context-aware firewall
- Identity-based services
- Failover options
- Cisco IOS firewalls and NAT
- CBAC
- Zone-based firewall
- Port-to-application mapping
- Identity-based firewalling
- Cisco Intrusion Prevention Systems (IPS)
- Cisco IOS IPS
- Cisco AAA protocols and application
- RADIUS
- TACACS+
- Device administration
- Network access
- IEEE 802.1X
- VSAs
- Cisco Identity Services Engine (ISE)
- Cisco Secure ACS Solution Engine
- Cisco Network Admission Control (NAC) Appliance Server
- Endpoint and client
- Cisco AnyConnect VPN Client
- Cisco VPN Client
- Cisco Secure Desktop
- Cisco NAC Agent
- Secure access gateways (Cisco IOS router or ASA)
- IPsec
- SSL VPN
- PKI
- Virtual security gateway
- Cisco Catalyst 6500 Series ASA Services Modules
- ScanSafe functionality and components
- Cisco Web Security Appliance and Cisco Email Security Appliance
- Security management
- Cisco Security Manager
- Cisco Adaptive Security Device Manager (ASDM)
- Cisco IPS Device Manager (IDM)
- Cisco IPS Manager Express (IME)
- Cisco Configuration Professional
- Cisco Prime
- Router hardening features (for example, CoPP, MPP, uRPF, and PBR
- Switch security features (for example, anti-spoofing, port, STP, MACSEC, NDAC, and NEAT)
- NetFlow
- Wireless security
- Network segregation
- VRF-aware technologies
- VXLAN
- VPN solutions
- FlexVPN
- DMVPN
- GET VPN
- Cisco EasyVPN
- Content and packet filtering
- QoS application for security
- Load balancing and failover
SECURITY POLICIES AND PROCEDURES, BEST PRACTICES, AND STANDARDS
- Security policy elements
- Information security standards (for example, ISO/IEC 27001 and ISO/IEC 27002)
- Standards bodies (for example, ISO, IEC, ITU, ISOC, IETF, IAB, IANA, and ICANN)
- Industry best practices (for example, SOX and PCI DSS)
- Common RFC and BCP (for example, RFC2827/BCP38, RFC3704/BCP84, and RFC5735)
- Security audit and validation
- Risk assessment
- Change management process
- Incident response framework
- Computer security forensics
- Desktop security risk assessment and desktop security risk management
SYSTEM HARDENING AND AVAILABILITY
- Routing plane security features (for example, protocol authentication and route filtering)
- Control Plane Policing
- Control plane protection and management plane protection
- Broadcast control and switch port security
- Additional CPU protection mechanisms (for example, options drop and logging interval)
- Disable unnecessary services
- Control device access (for example, Telnet, HTTP, SSH, and privilege levels)
- Device services (for example, SNMP, syslog, and NTP)
- Transit traffic control and congestion management
THREAT IDENTIFICATION AND MITIGATION
- Identify and protect against fragmentation attacks
- Identify and protect against malicious IP option usage
- Identify and protect against network reconnaissance attacks
- Identify and protect against IP spoofing attacks
- Identify and protect against MAC spoofing attacks
- Identify and protect against ARP spoofing attacks
- Identify and protect against DoS attacks
- Identify and protect against DDoS attacks
- Identify and protect against man-in-the-middle attacks
- Identify and protect against port redirection attacks
- Identify and protect against DHCP attacks
- Identify and protect against DNS attacks
- Identify and protect against MAC flooding attacks
- Identify and protect against VLAN hopping attacks
- Identify and protect against various Layer 2 and Layer 3 attacks
- NBAR
- NetFlow
- Capture and utilize packet captures
INTRUSION PREVENTION AND CONTENT SECURITY
- Cisco IPS 4200 Series Sensor appliance and Cisco ASA appliance IPS module
- Initialize the sensor appliance
- Sensor appliance management
- Virtual sensors on the sensor appliance
- Implement security policies
- Promiscuous and inline monitoring on the sensor appliance
- Tune signatures on the sensor appliance
- Custom signatures on the sensor appliance
- Actions on the sensor appliance
- Signature engines on the sensor appliance
- Use Cisco IDM and Cisco IME to manage the sensor appliance
- Event action overrides and filters on the sensor appliance
- Event monitoring on the sensor appliance
- VACL, SPAN and RSPAN on Cisco switches
- Cisco WSA
- Implement WCCP
- Active Directory integration 3.3.c Custom categories
- HTTPS configuration
- Services configuration (web reputation)
- Configure proxy bypass lists
- Web proxy modes
- Application visibility and control
- Identity-based AAA
- Cisco router and appliance AAA
- RADIUS
- TACACS+
- Device administration (Cisco IOS routers, Cisco ASA, and Cisco ACS5.x)
- Network access (TrustSec model)
- Authorization results for network access (ISE)
- IEEE 802.1X (Cisco ISE)
- VSAs (Cisco ASA, Cisco IOS, and Cisco ISE)
- Proxy authentication (Cisco ISE, Cisco ASA, and Cisco IOS)
- Cisco ISE
- Profiling configuration (probes)
- Guest services
- Posture assessment
- Client provisioning (CPP)
- Configure Microsoft Active Directory integration and identity sources
PERIMETER SECURITY AND SERVICES
- Cisco ASA firewalls
- Basic firewall Initialization
- Device management
- Address translation
- ACLs
- IP routing and route tracking
- Object groups
- VLANs
- Configure EtherChannel
- High availability and redundancy 5.1.j Layer 2 transparent firewall 5.1.k Security contexts (virtual firewall)
- Cisco Modular Policy Framework
- Identity firewall services
- Configure Cisco ASA with ASDM
- Context-aware services
- IPS capabilities
- QoS capabilities
- Cisco IOS zone-based firewall
- Network, secure group, and user-based policy
- Performance tuning
- Network, protocol, and application inspection
- Perimeter security services
- Cisco IOS QoS and packet-marking techniques
- Traffic filtering using access lists
- Cisco IOS NAT
- uRPF
- Port to Application Mapping (PAM)
- Policy routing and route maps
- IKE (v1/v2)
- IPsec LAN-to-LAN (Cisco IOS and Cisco ASA)
- DMVPN
- FlexVPN
- GET VPN
- Remote-access VPN
- Cisco EasyVPN Server (Cisco IOS and Cisco ASA)
- VPN Client 5.X
- Clientless WebVPN
- Cisco AnyConnect VPN
- Cisco EasyVPN Remote
- SSL VPN gateway
- VPN high availability
- QoS for VPN
- VRF-aware VPN
- MAC sec
- Digital certificates (enrollment and policy matching)
- Wireless access
- EAP methods
- WPA and WPA2
- wIPS
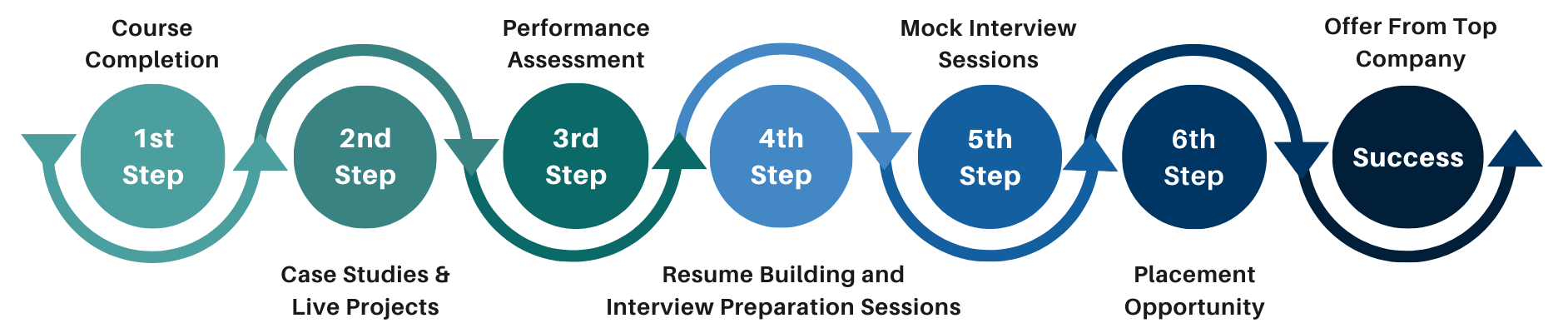
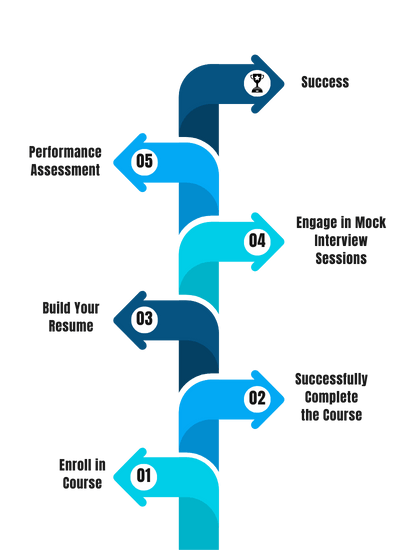
Our Process
FAQ'S
- Classroom Training
- Online Training
- Corporate Training
- On campus Training
Career Assistance
- Build an Impressive Resume
- Attend Mock-Up Interviews with Experts
- Get Interviews & Get Hired
Training Certification
Earn your certificate
Your certificate and skills are vital to the extent of jump-starting your career and giving you a chance to compete in a global space.
Share your achievement
Talk about it on Linkedin, Twitter, Facebook, boost your resume or frame it- tell your friend and colleagues about it.
Upcoming Batches
What People Say
Our Partners
Need Customized Curriculum? Request Now
Structure your learning and get a certificate to prove it.
Our Clients

Our Placed Students
Related Courses
Review Us
Neha Sharma
![]() Friday, 05 May 2017
Friday, 05 May 2017
CCIE Security In Noida
I have completed my training from CETPA. It was the good experience because I have learned lots of things . It helped me to improve my skills and knowledge because of this now I am placed in a very good company and all this happened because of cetpa. I just want to thanks to all the staff of the Cetpa.
Course Features
- Lectures 0
- Quizzes 0
- Duration 10 weeks
- Skill level All levels
- Language English
- Students 0
- Assessments Yes